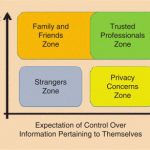
Young people’s unique understandings and perspectives are often not considered in debates and discussions around privacy and security. This article outlines a youth-centric notion of digital privacy and guiding principles around privacy developed by young people from Antigua and Barbuda, Australia, Ghana, and Slovenia.




















 JOIN SSIT
JOIN SSIT